Sales Development Infrastructure for Cybersecurity
Embedded SDR teams for cybersecurity vendors - built for long sales cycles, technical buyers, and the need for quality over volume. We've been doing this since 2017.
We've built pipeline for clients across cybersecurity sub-verticals, including:
Cloud SIEM solutions
Threat intelligence platforms
DNS security
Endpoint detection & response (EDR)
Identity & access management (IAM)
When cybersecurity teams turn to Sellerate
Cybersecurity sales require deep technical context, multi-threaded outreach, and brand-safe execution - not spray-and-pray tactics.
Long, complex sales cycles demand sustained engagement
Cybersecurity deals take months (sometimes quarters) to close. You need an SDR who can stay engaged, multi-thread across personas, and maintain context over time - not someone chasing quick meetings.
Technical buyers expect relevance and credibility
CISOs and security leaders can spot generic outreach instantly. You need messaging that reflects understanding of their environment, threats, and priorities - not templates blasted to thousands.
Expansion into new regions or verticals
You're growing into EMEA, LATAM, or APAC, or targeting a new vertical (financial services, healthcare, manufacturing). You need local or vertical-specific capacity without hiring full teams.
Events and field marketing need pipeline follow-through
You sponsor high-value events but struggle to convert attendance into pipeline. You need coordinated pre-event outreach and disciplined post-event follow-up - not just badge scans.
Brand safety and compliance matter
In cybersecurity, your outbound motion reflects your security posture. You can't afford sloppy execution, list burns, or deliverability issues that damage credibility.
Trusted by teams at leading cybersecurity companies













Buyer personas we engage in cybersecurity
Cybersecurity deals are multi-threaded—here are the core roles we typically engage
CISO / VP Security
Executive-level buyers focused on risk, vendor credibility, and board-level outcomes. Messaging must be strategic, not tactical—and earn trust quickly.
SOC / Security Operations leaders
Operators who care about speed, workflow fit, and measurable impact on security operations. They respond to specificity, not generic “better security” claims.
Compliance / GRC leaders
Stakeholders responsible for audits, controls, and regulatory readiness. They look for clarity, process, and outcomes that reduce compliance burden.
PROCESS
How it works in cybersecurity
A structured approach that respects long cycles, technical buyers, and the need for credibility.
OUR INFRASTRUCTURE
What you get when scaling
Add capacity without compromising the quality and consistency already driving your pipeline.

EMBEDDED SDRs
In-house execution, embedded
A dedicated SDR (or team) operating under your brand, exclusive to your account. They learn your product, positioning, ICP, and sales process -f and align daily with your stakeholders so messaging and targeting stay sharp. All SDRs are bilingual at minimum (Spanish/English, Portuguese/English, German/English, and more), making us a natural fit for regional expansion.
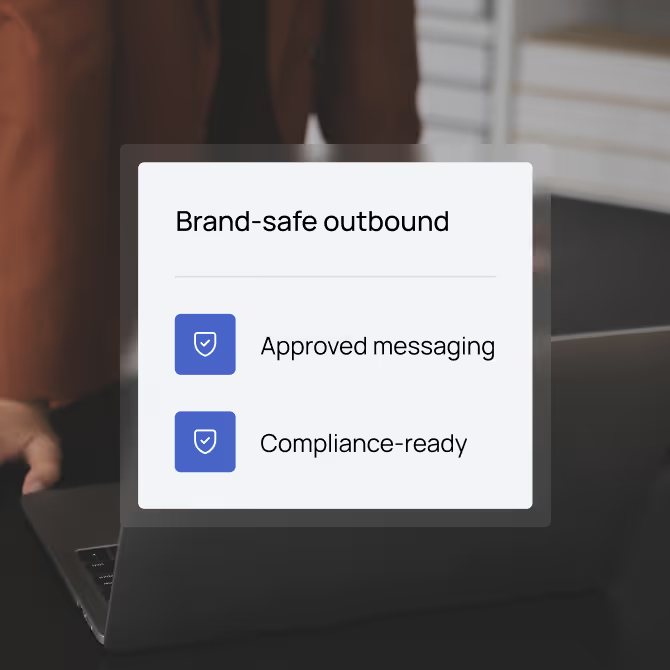
ACCOUNT MANAGERS
Execution aligned, decisions unblocked
Your account manager runs weekly syncs, owns the reporting cadence, and acts as the bridge between your team and the SDR.
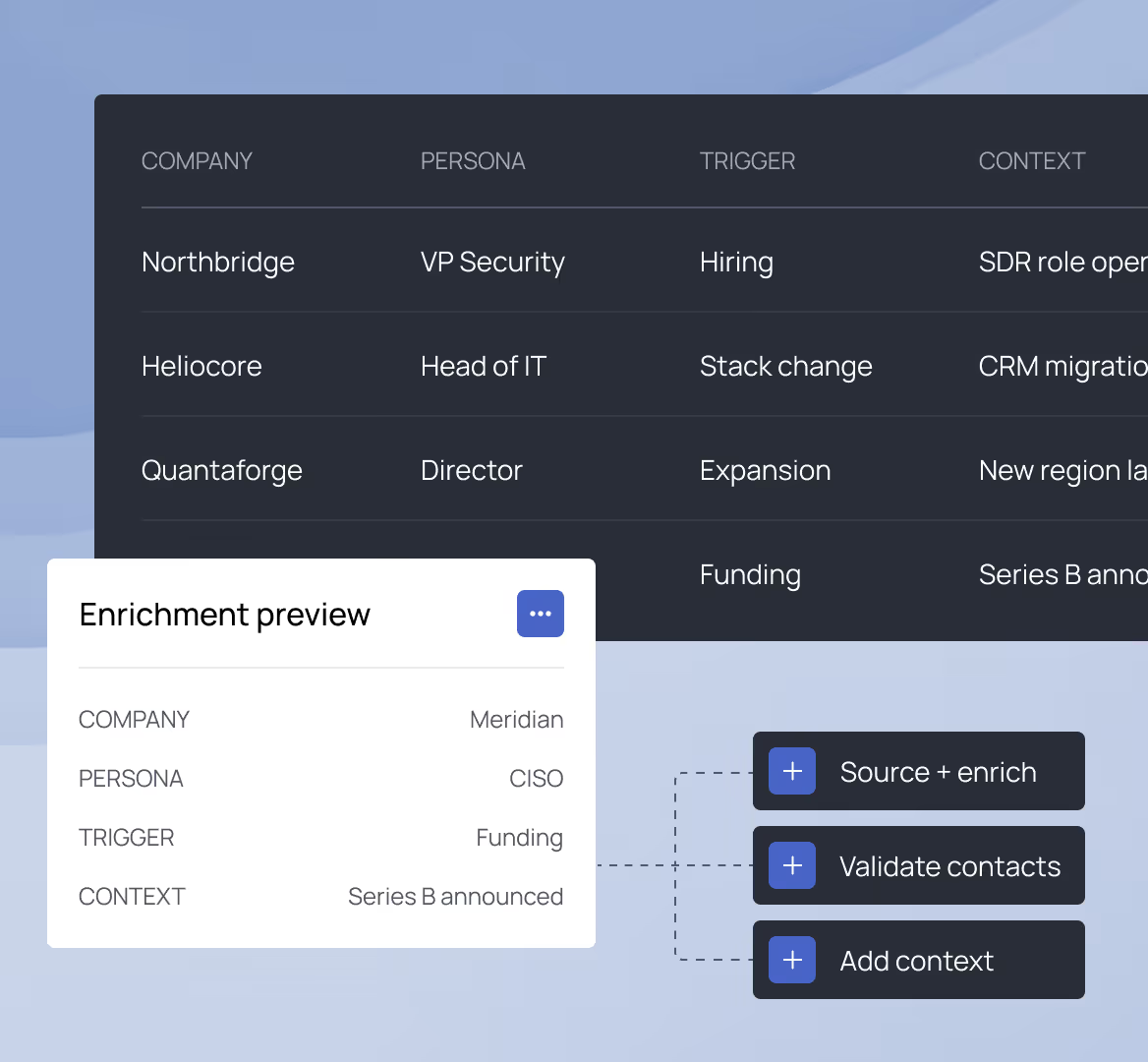
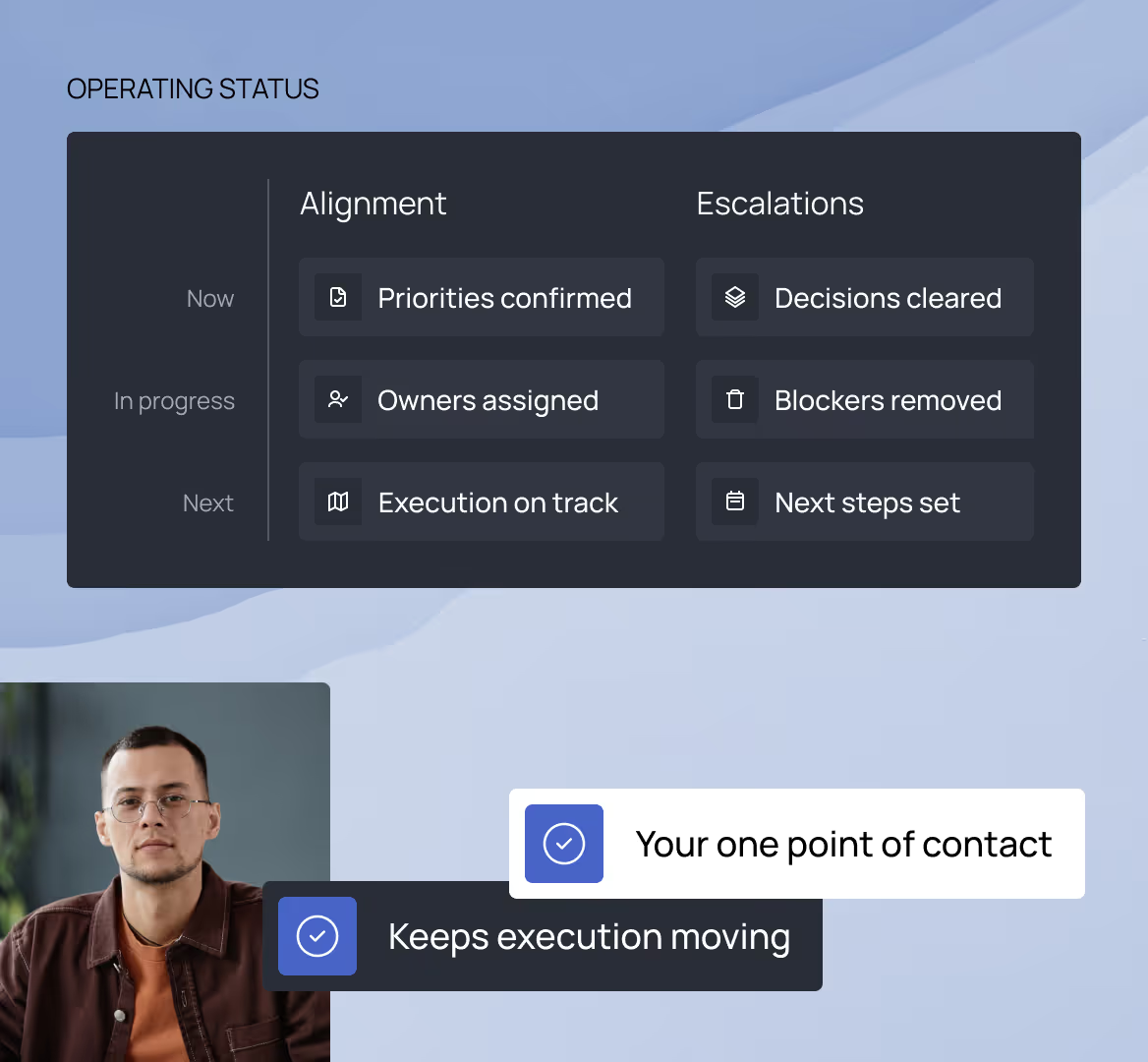
DATA TEAM
Data team
Targeting, sourcing, and enrichment - powered by AI - so outreach is built on strong data and relevant context, not guesswork. Better targeting reduces noise, improves response rates, and protects your brand.
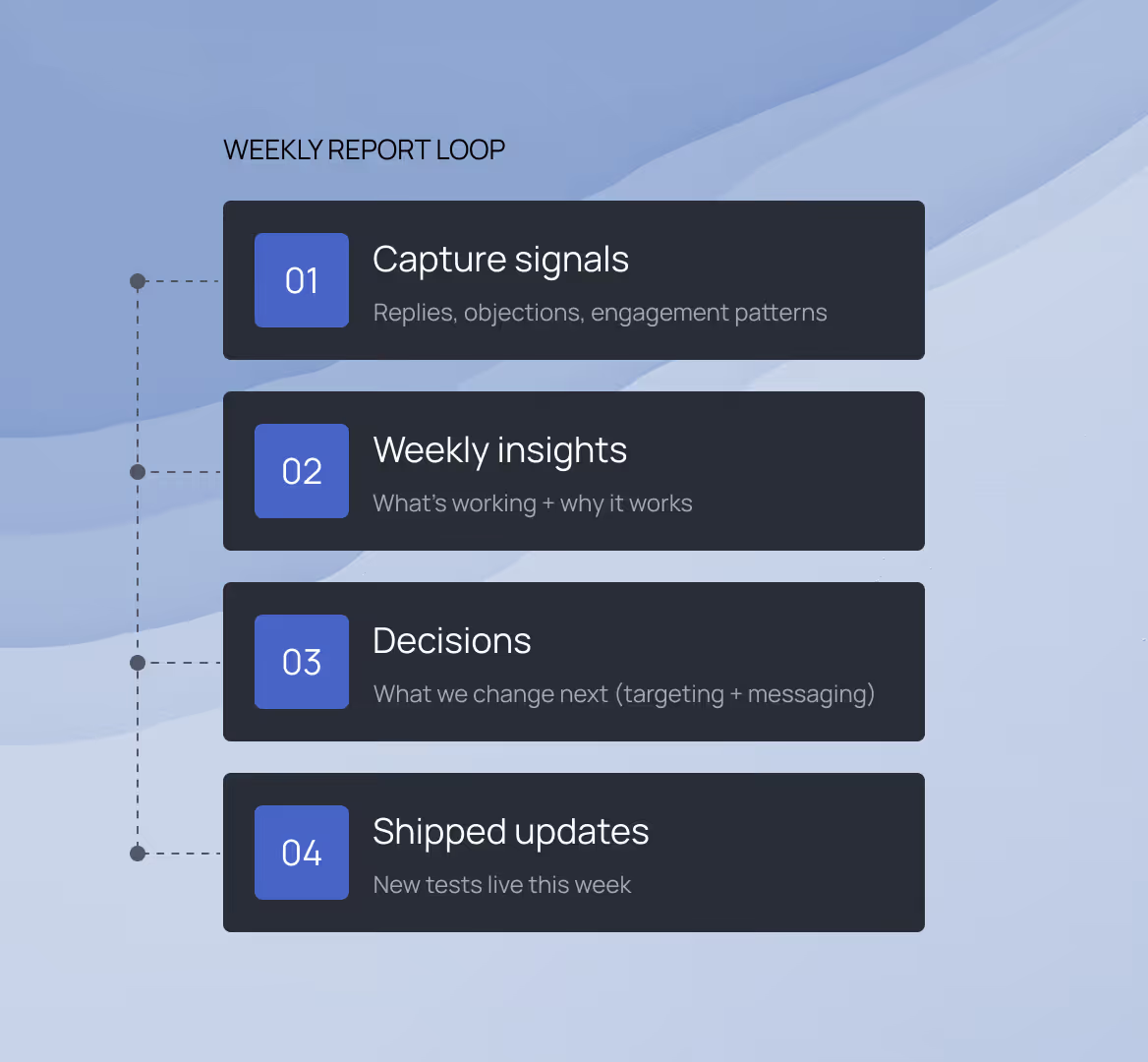
REPORTING
Insights & reporting
Structured reporting on activity, learnings, and outcomes - not vanity metrics. Clear visibility into what's working, what's not, and what we're changing next, so execution is never a black box.

LEARNING & DEVELOPMENT
Continuous improvement, built in
Continuous coaching, call reviews, and messaging iteration so the SDR gets sharper over time. This includes structured onboarding, ongoing training, and skill development - so performance improves, not plateaus.
TECH STACK
Full tooling, no procurement
We handle the tooling and integrations needed to run the motion efficiently - CRM, outreach platforms, data enrichment, and automation. You get access to our full stack without additional costs or procurement complexity. Below are the core tools we use and maintain internally.
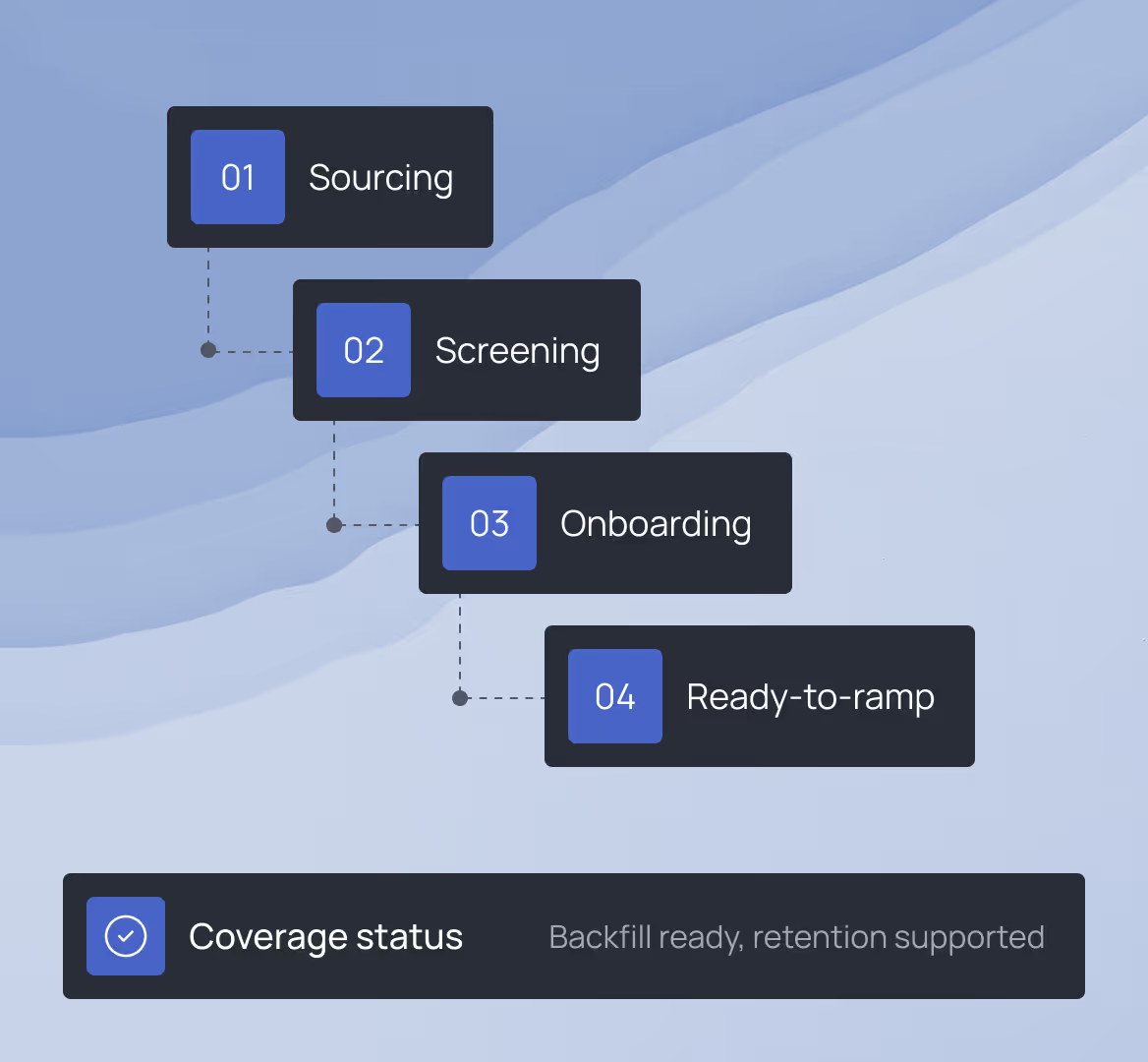
RECRUITING ENGINE
Always staffed, always supported
The hiring and retention machine that keeps SDR capacity strong and consistent as you scale. We handle recruiting, onboarding, and retention so you never have to worry about backfilling or managing SDR churn.

AI-POWERED INFRASTRUCTURE
Sellerate AI
A Slack-native AI agent built into the SDR's daily workflow. Coaches outreach using your ICP and messaging guidelines, researches prospects by combining your knowledge base with live web intelligence, and generates account briefs in-thread - in seconds. Not a separate tool. Part of the infrastructure.
STATS
Supporting cybersecurity teams since 2017
8+ yr
Serving cybersecurity clients from around the world
+30
Average engagement length in cybersecurity industry
24 mo
How do you handle technical complexity in cybersecurity outreach?
The embedded SDR learns your platform, competitive positioning, and buyer pain points through close collaboration with your team. We don't use generic templates - messaging is tailored to technical buyers and their specific environments.
Can you support multi-persona outreach (CISO, SOC, GRC, procurement)?
Yes. Cybersecurity deals are multi-threaded by nature, so we target multiple personas with messaging tailored to each role and decision stage.
How do you protect our brand and avoid spammy outreach?
We operate quality-first with targeting discipline and messaging standards. In cybersecurity, your outbound motion reflects your security posture - we treat that seriously.
Can you support event-driven campaigns?
Yes. We coordinate pre-event targeting to drive attendance and post-event follow-up to convert engagement into qualified pipeline. Event support is a common use case in cybersecurity.
How fast can we start?
Onboarding and training typically take two to four weeks. Once execution starts, you'll see pipeline activity from week one. Cybersecurity cycles are long, so we focus on building sustained engagement - not quick wins.
Do you work with compliance and data privacy requirements?
Yes. We align with your compliance standards and can work within specific data handling, GDPR, or regional requirements as needed.
Ready to build pipeline in cybersecurity?
Book a call and we'll discuss your ICP, your sales motion, and how Sellerate's embedded model would work for your team.
What happens next
Fit check - your ICP, buyer personas, and sales cycle
Map target accounts, personas, and outreach approach
Recommended rollout plan with timeline and ramp structure